Technical Articles
March 11, 2026
Hardening the Core: Beyond the “Security Plugin” Illusion
There is a dangerous misconception in the web development ecosystem, particularly within WordPress, that installing a “Security Plugin” makes your site secure. In reality, adding more PHP code (in the form of a heavy plugin) often increases your attack surface rather than reducing it.
True cybersecurity requires a “Zero-Trust” mindset applied at the server and architectural levels, long before a request ever reaches the application layer.
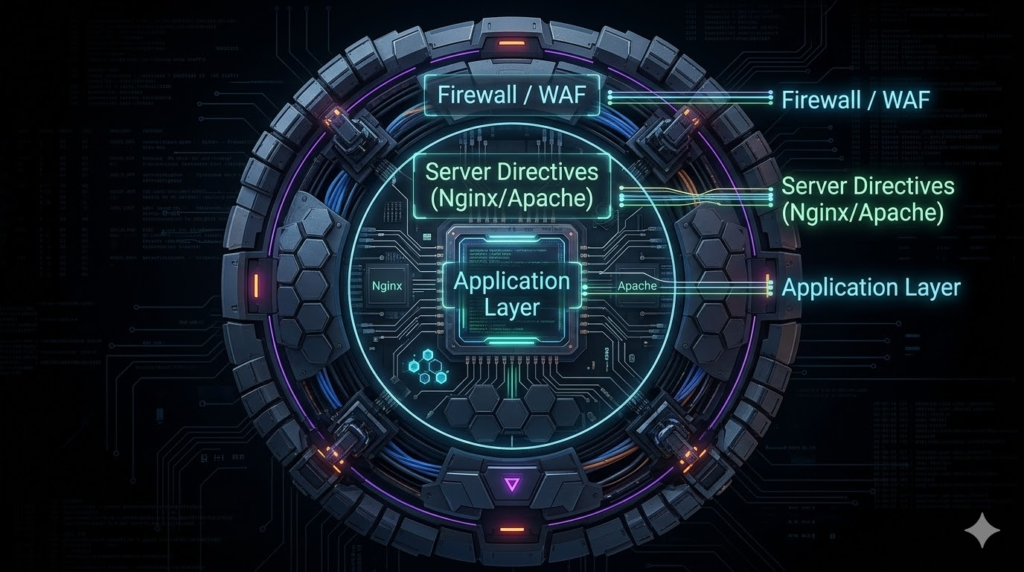
The Multi-Layered Defense Protocol:
- Server-Level Hardening: Utilizing Nginx or Apache directives to block malicious payloads at the edge. If an exploit tries to execute a PHP script inside the
/uploads/directory, the server should instantly drop the connection—no plugin required. - Disabling XML-RPC: A notorious vector for brute-force attacks and DDoS amplification. Unless explicitly required by an external app, it must be terminated.
- Strict File Permissions: Ensuring that the web server has the absolute minimum permissions necessary to function, preventing unauthorized file modifications even if the application is compromised.
The Verdict
Security cannot be installed via a .zip file. It must be woven into the fabric of the server architecture. Proactive hardening ensures that your digital assets remain bulletproof against automated bots and targeted exploits alike.
[PROCESS TERMINATED WITH EXIT CODE 0]